Because Security Comes First
AAA Authentication
AAA Authentication
Solutions for Data Security Management

AAA Authentication
GA Soft Tech leverages its strong expertise in authentication algorithms and encryption methodologies to offer security services based on 3-factor authentication. Our proprietary 3 Factor Authentication solutions enable enterprises and educational institutions to exercise complete control and monitoring over its networks and IT infrastructure and eliminates potential security threats to a greater extent.
Anytime, Anywhere Access
Laptops, tablets and other devices connected to the internet are increasingly becoming the first choice of devices for employees in enterprises and students and staff across schools and universities.
Data Security Management
Owing to the ‘Bring/Choose Your Own Device’ and the ‘Corporate Owned, Personally Enabled’, organizations need to prioritize effective data security management for preventing data breaches, malware intrusion, and unauthorized access.
Why is Secure Access to Networks the Need of the Hour?
“A survey revealed that 87% of companies bank on their employees using their own devices to access business applications.”
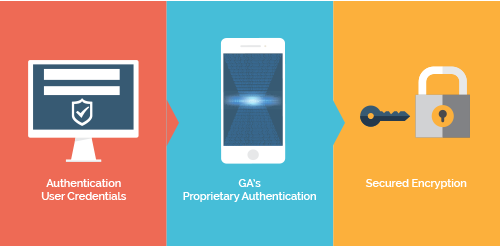
Working of 3 Factor Authentication
Our 3 FACTOR authentication technique is based on linking the physical identity of the user to the server in order to secure the critical systems of the organization. This user-based authentication method not only helps prevent financial frauds and data/identity thefts but also helps identify and nab routine cybercriminals.
User Verification Parameters
- Unique biological characteristics (Biometrics)
- Something only the user knows (user id and password)
- Something only the user has (mobile phone/ landline/ hard token)
GA Soft Tech’s
AAA Authentication Solutions
GA Soft Tech’s 3 Factor Authentication model is based on a three-stage identification method. This involves the verification of the user ID and password at the active directory level, followed by the authentication of a randomly generated One Time Password (OTP) along with the 3-factor proprietary verification.
3 Levels of Verification